In an interconnected business world, data is in continuous motion between systems, devices and users. Although this connectivity enhances efficiency the risk of unauthorized access also becomes high. Malicious information may be revealed without the necessary protection and result in both financial and operational losses. This is where network security on computer networks becomes critical. It sets up protective features that govern access to data as well as system usage.
Understanding Unauthorized Access
Unauthorized access takes place when a person or system is able to enter a network without authorization. This may occur as a result of a feeble password, obsolete systems, or malicious attacks. The main objective of network security in computer networks is to avoid such incidences by making sure that only authorized users and gadgets can communicate with the system.
Network security within computer networks lowers the risk of breaches and ensures integrity of systems by establishing clear access control and tracking of system activity.
Authentication Mechanism Role
The first line of defense is authentication. It checks the identity of users and then gives access. Computer networks employ passwords, multi-factor authentication, and biometric verification as some of the methods of network security to make sure that only authorized people can log in.
These steps provide several layers of protection. Although a single tier may be compromised, more layers will protect against unauthorized access. This enhances network security in computer networks against typical threats.
Significance of Access Control Systems
After a user is authenticated access control is what is permitted to be done. All data or systems are not required to all users. Computer networks Network security is a strategy that gives users access to computer networks based on job assignments, which is known as role-based access control.
This restricts exposure and only the people who require it are able to access sensitive information. Network security in computer networks reduces the threat of both internal and external attacks by limiting access.
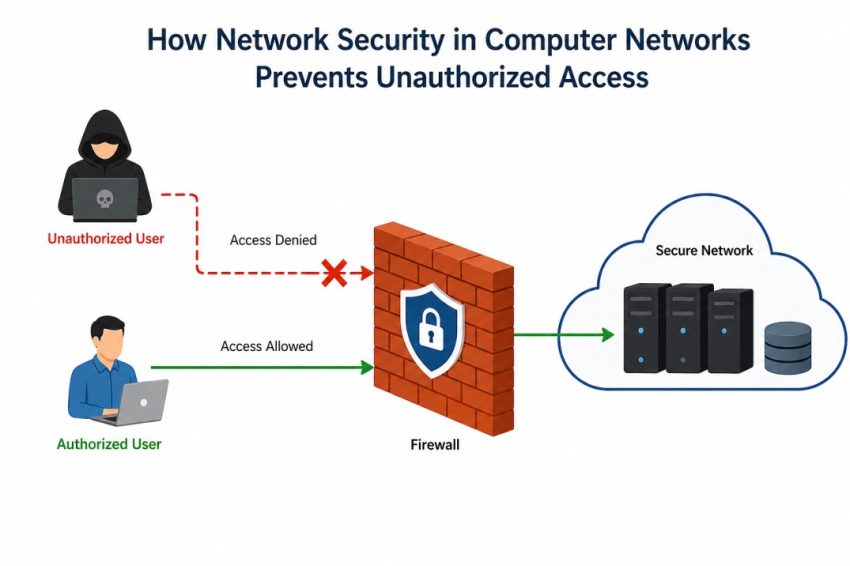
Firewalls and Encryption
Firewalls are designed to provide barriers between trusted and untrusted networks. They monitor inbound and outbound traffic and prevent suspicious behavior. Moreover, encryption secures data by transforming it into a secure form that cannot be easily deciphered.
The combination of these tools enhances the security of networks within computer networks since even when interception of data takes place, it is still secured. Firewalls eliminate unauthorized access, and encryption secures information when being transmitted.
Nonstop Surveillance and Detection of Threats
It is not a one-time task to prevent unauthorized access. It involves continuous observation and prompt action towards any possible threats. Network security within computer networks encompasses mechanisms which monitor user activity and identify abnormal behavior.
In the case of any suspicious activity detected, there would be alerts and prompt actions can be undertaken. This can be proactive and can be used to prevent threats before they can do a lot of harm and ensure the network is secured at all times.
Frequent Updates and Maintenance
Attackers typically use out-of-date software and systems as entry points. In computer networks, regular updates and maintenance are critical elements in network security. With a current system, businesses are able to correct vulnerabilities and enhance the general protection.
Routine checks also provide security measures to be up to date with the changing threats. This continual work helps to provide a good protection against unauthorized access.
Awareness and Training of Employees
Security breaches are often predominantly caused by human error. There is a chance that employees provide sensitive information without knowing it or become a victim of phishing. Network security within computer networks involves training programs which educate users on the safe practices.
Through creating awareness, organizations will minimize the chances of errors that may result in unauthorized access. A knowledgeable workforce will be a valuable component of the security system.
Conclusion
The control of unauthorized access will need a combination of technology, processes and awareness. All these are taken care in network security in computer networks through implementing authentication, access control, monitoring and regular updates. It assures that the systems and data are only accessed by authorized users. Strong security practices are a must in a time when digital threats are on the rise and can be used to safeguard business operations and ensure trust.
Also Read: Common Mistakes to Avoid While Using Free Data Recovery Software for Windows 10